Error accessing a script generated by PHP.
I was trying to move a script to a new server for a client. The script in question is the “Member Login Script” by PHPJabbers. However, the error is independent of the script and occurs when the server returns a different mime type as a document than expected. In this specific case, the following error appeared in the browser’s error console:
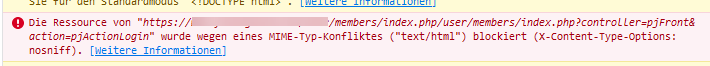
The resource of "/user/members/index.php/user/members/index.php?controller=pjFront&action=pjActionLogin"
was blocked because of a MIME type conflict ("text/html") (X-Content-Type-Options: nosniff).
The resource or the PHP spits out a Java script and is included with a <script> tag. The type “text/javascript” is expected here, but the HTTP header specifies that “text/html” is delivered by the script.
What is the “nosniff” header
?
Brief definition:
The “X-Content-Type-Options: nosniff” header is an HTTP header sent by web servers to instruct the browser not to guess the MIME type of a document and instead use the MIME type provided by the server. This means that the browser does not interpret the document as a different type than intended by the server.
This is important to avoid security problems that can be caused by so-called “MIME sniffing”. MIME sniffing is a behaviour of browsers where they try to guess the MIME type of a document if it has not been explicitly specified by the server. This can lead to security problems, as an attacker can provide a document with a MIME type that is considered more secure by the browser than the actual MIME type of the document.
By sending the “X-Content-Type-Options: nosniff” header, a web server can prevent browsers from interpreting documents with an incorrect MIME type and thus avoid security problems.
Problem solution
The background is therefore a server configuration. This can now either be changed, e.g. via HtAccess:
<IfModule mod_headers.c>
Header always set X-Content-Type-Options "nosniff"
</IfModule>
However, this did not work for me. Either the corresponding module was not installed or .htaccess files were simply deactivated.
In my case, I helped myself by writing a proxy script:
<?php
header("Content-Type: text/javascript");
$content = file_get_contents("/user/members/index.php?controller=pjFront&action=pjActionLogin");
echo $content;
This first sets the correct header, then the script is read in and simply output. Afterwards, the script worked and the login appeared.